
Request and Response for user registration

Request for user login

Login confirmation
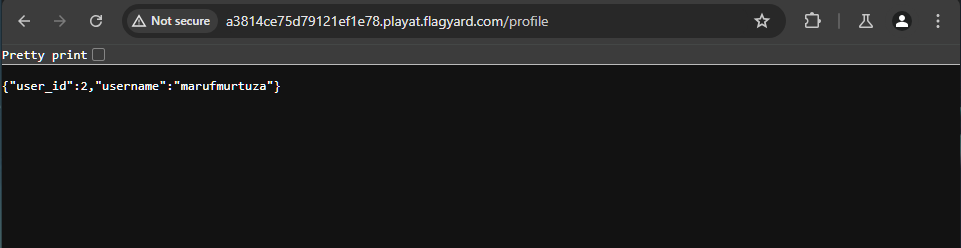
User profile

Successful file upload
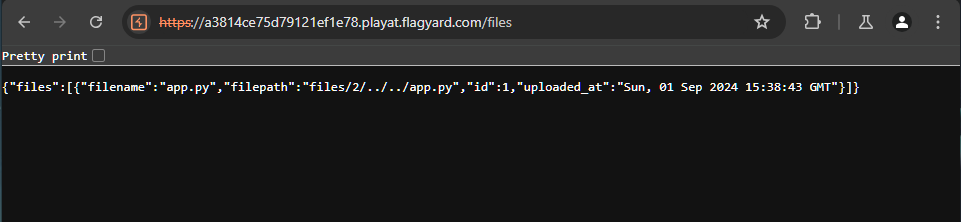
Uploaded file details

Admin credentials found via LFI

Request for login into the admin account

Flag found

Request and Response for user registration

Request for user login

Login confirmation
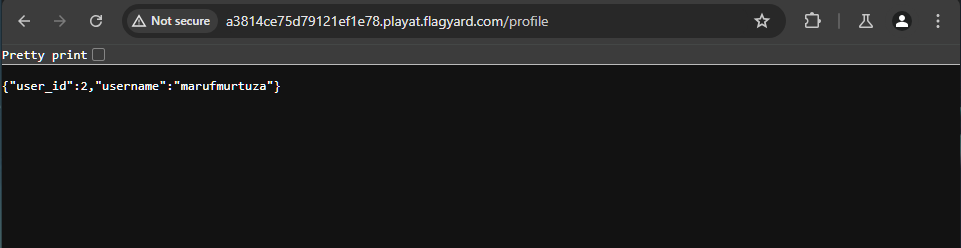
User profile

Successful file upload
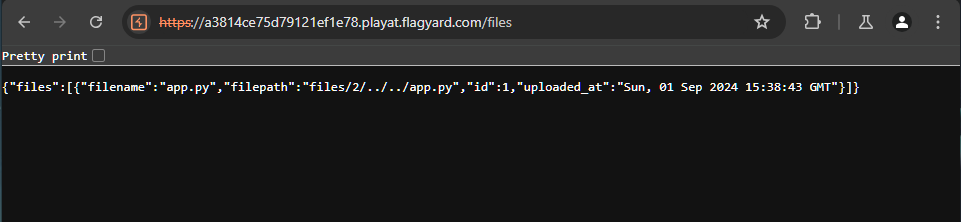
Uploaded file details

Admin credentials found via LFI

Request for login into the admin account

Flag found